A while ago I had a request from one of my clients to monitor their new Fortigate Firewalls, as there is no existing management pack for this it required a bit of custom work.
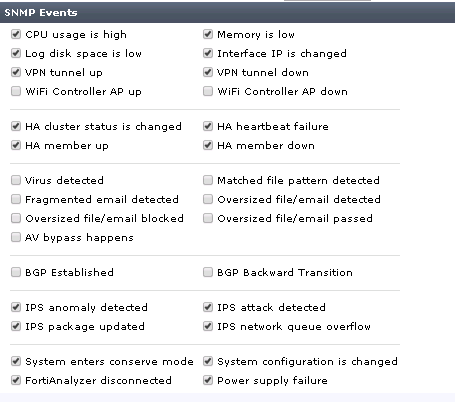
First on the firewall you’ll also need to configure SNMP, as well as what trap notifications will be sent.
Then discover the Fortigate using the standard network monitoring discovery.
This is the address for the Fortigate MIB file contents which you will need in order to map OIDs for the next part.
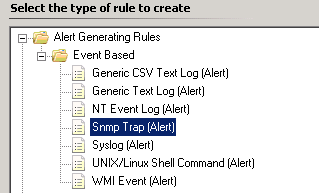
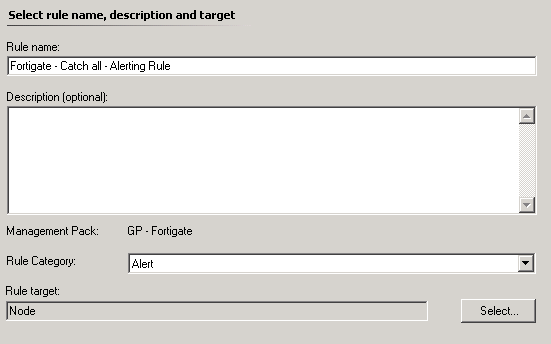
In SCOM create an SNMP Trap alerting Rule targeting the Node Class.
For now leave the OID properties filter empty
This rule will be used to identify any OIDs in the future that may be missing from your specific alerting rules.
Now using the MIB list provided earlier each alert ticked in the Fortigate configuration needs to be mapped to the relevant OID and a specific alerting rule created for it, for example 1.3.6.1.4.1.12356.101.4.4.2.1.2 is the OID for HIgh Processor Usage. So in order to generate an alert for High CPU on the Fortigate you will need a rule with this specific OID in the filter 1.3.6.1.4.1.12356.101.4.4.2.1.2.
Repeat for each OID that you need to monitor and use the catch all to identify anything you may have missed.
![]()

i’m new to MIB stuff. any free tool we can read the MIB files?
Hi Steven,
There are a few, I normally just google for mib reader when I need one. I used snmpb the last time.
If I’d like to monitor the CPU, I have to create a rule which generates an alert when the OID 1.3.6.1.4.1.12356.101.4.4.2.1.2 is catched. There is no option to set a threshold, when the alert should be raised (for example CPU is >80%). Basically I only can raise alerts, when the FW is sending a specific OID. Did I unterstand this correctly?
If yes, how can I determine when the Fortigate completly crashed? I guess there isn’t sent any OID when this happes…
Hi Stephan,
You are correct, the source of the trap in this case the firewall should have configuration as to when the traps are sent i.e. a high CPU condition.
As for if the device crashes there is a built in alert for when an snmp monitored device becomes unavailable.
Hi Warren,
thank you for the information. I could configure SCOM to monitor my Fortigate unit.
One more question: do you know, when a “System configuration is changed” event is sent via SNMP? I’ve enabled the checkbox for this but there is nothing sent to SCOM when I changed the name of a IPv4 policy. Aren’t there always sent events when a change is made?
Hi Stephan.
I’m unfortunately not familiar with the Fortigate side of the configuration. I can suggest setting up a ‘catch all’ rule or using snmp trap tracing, in conjunction with turning on all of the snmp traps to see if you can catch the ipv4 policy change.
Hello Warren,
I know this is quite an old article but I’m trying to get our FortiGate’s in SCOM.
I have created the “Catch All” rule but I’m only getting 2 OIDs back:
1.3.6.1.4.1.12356.101.2.0.602 (fgTrapAvOversize)
1.3.6.1.4.1.12356.101.2.0.607 (fgTrapAvOversizePass)
We are migrating from PRTG to SCOM, but in PRTG there is an OID for a sensor but also limits, I don’t see that back in your article.
Is this still the way to get FortiGates in SCOM or is there a “newer” way to do that?
Hi Chris,
I haven’t had to monitor a FortiGate for many year but the method should still work. Are you able to confirm that other traps are being sent for different events?